
Audits and regulatory examinations are inevitable in the financial industry. GRC audit findings don’t need to be, but as banking services grow more sophisticated and compete at fever pitch, you might find yourself postponing that risk assessment meeting to focus on your new digital banking platform release. Maybe the new release has caused an increase in customer calls and now you also need to postpone your InfoSec Committee meeting to support your teams. Next thing you know, it’s audit time and you are not prepared.
I am reminded of my teenage years, when cleaning my bedroom was a chore and a daily battle. “How can you find anything in this room?” my parents would say. “Please clean your room.” I’d respond, “I know where everything is,” or “I’ll do it later. It’s just my room, nobody is coming to see it.” Back and forth we’d go until the day I wasn’t allowed to attend that much-anticipated party because I needed to clean my room. The horror of being the only one in our class to miss it, if only I’d done as they asked the first time.
How often have we found ourselves in a similar situation at work? The fact is that risk assessments, policy reviews, business continuity planning, and similar proactive tasks often take a lower priority when they compete with client-facing and daily operational activities. We may think “customers aren’t coming to see those.” But these proactive tasks are the proverbial “necessary evil” and usually the topic of audit findings for being ineffective, incomplete, or inappropriate.
These are examples of GRC audit findings we can avoid if we take a proactive approach:
Access Controls – Administrative Accounts
“Weak password criteria and management of default administrator accounts.”
Information Security Program
“Information Security Policy does not fully document activities or include processes which are repeatable and measurable.”
Governance
“No comprehensive metrics to evaluate the effectiveness of the Information Security Program and provide early indication of a breakdown in the control environment.”
I have seen this often throughout my career as an information security practitioner working with banks and credit unions. Sometimes it really is necessary to postpone that access review or risk assessment. Maybe it’s just another hat we wear and it’s difficult to carve out the time. Maybe we depend on others who also wear other hats and may have conflicting priorities. The challenge of doing policy/access reviews or risk assessment work is completing the task, not just because we have an upcoming audit, but because it’s a regulatory expectation to be an ongoing activity.
Now is a good time to re-evaluate your reactive approach to information security. Below are some practical ways to use your security and GRC building blocks to make your IT security, risk, compliance, vendor, and business continuity programs more effective and avoid findings in your next audit/exam.
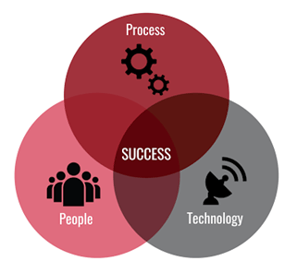
We often talk about the concept of people, process, and technology (PPT) in Operations. A framework introduced in the 1960s to drive organizational change and efficiency, it still applies today in IT, risk management, and information security. The right combination of people, processes and technology is important to deliver innovative financial products and services to the market. Equally important, and a regulatory expectation, is the need to protect the confidentiality, integrity, and availability of the information managed with financial products and services.
Enter governance, risk, and compliance, which provides the structure to accomplish information security by aligning:
People in the right roles can determine the appropriate processes to manage your enterprise programs. With appropriate processes in place, you can standardize and scale your operations. Using technology, you can then automate these processes to support growth and provide greater visibility and accountability.
This is sometimes easier said than done. However, taking the time to set these up properly will provide a strong foundation to manage your programs, complete your tasks and be well prepared for your next audit.
On June 30, 2021, the FFIEC announced a new “Architecture, Infrastructure, and Operations (AIO)” booklet in the examination handbook series. The booklet outlines regulatory “…expectations regarding architecture and infrastructure planning, governance and risk management, and operations of regulated entities. The booklet discusses the interconnectedness among an entity’s assets, processes, and third-party service providers…”
Of note in this and the subsequent release of the “Authentication Guidance” on August 11, 2021, the FFIEC makes it clear that banks and credit unions must ensure proper governance of IT and information security, especially the risk of unauthorized users accessing internal networks and digital banking systems. The guidance talks about the importance of properly documenting roles and responsibilities for information security as well as AIO management. It also provides examples of best practices for authentication controls and clearly states the importance of asset inventories and risk assessments. We expect this to be the focus of the next set of regulatory examinations coming to a city near you.
Some practical tips to avoid findings in your next GRC audit:
Ensuring GRC audit success takes a little bit of effort at first. The goal should be to create processes you can Rinse and Repeat. Start with proper/current documentation. This is the biggest weakness in information security programs. Even if done well the first time, it’s important to have a continuous process to keep all documentation current at established intervals. Transparency is key because in the end it’s all about protecting what’s important.
Source:
“Architecture, Infrastructure, and Operations (AIO)”: FFIEC: https://www.ffiec.gov/press/pr063021.htm
Stay up to date with the latest people-inspired innovation at Jack Henry.
.svg)
Learn more about people-inspired innovation at Jack Henry.
Who We Serve
What We Offer
Who We Are